Hundreds of Microsoft Azure accounts, some belonging to senior executives, are being targeted by unknown attackers in an ongoing campaign that's aiming to steal sensitive data and financial assets from dozens of organizations, researchers with security firm Proofpoint said Monday.
The campaign attempts to compromise targeted Azure environments by sending account owners emails that integrate techniques for credential phishing and account takeovers. The threat actors are doing so by combining individualized phishing lures with shared documents. Some of the documents embed links that, when clicked, redirect users to a phishing webpage. The wide breadth of roles targeted indicates the threat actors’ strategy of compromising accounts with access to various resources and responsibilities across affected organizations.
“Threat actors seemingly direct their focus toward a wide range of individuals holding diverse titles across different organizations, impacting hundreds of users globally,” a Proofpoint advisory stated. “The affected user base encompasses a wide spectrum of positions, with frequent targets including Sales Directors, Account Managers, and Finance Managers. Individuals holding executive positions such as “Vice President, Operations,” "Chief Financial Officer & Treasurer," and "President & CEO" were also among those targeted.”
Once accounts are compromised, the threat actors secure them by enrolling them in various forms of multifactor authentication. This can make it harder for victims to change passwords or access dashboards to examine recent logins. In some cases, the MFA used relies on one-time passwords sent by text messages or phone calls. In most instances, however, the attackers employ an authenticator app with notifications and code.
Proofpoint observed other post-compromise actions including:
- Data exfiltration. Attackers access and download sensitive files, including financial assets, internal security protocols, and user credentials.
- Internal and external phishing. Mailbox access is leveraged to conduct lateral movement within impacted organizations and to target specific user accounts with personalized phishing threats.
- Financial fraud. In an effort to perpetrate financial fraud, internal email messages are dispatched to target Human Resources and Financial departments within affected organizations.
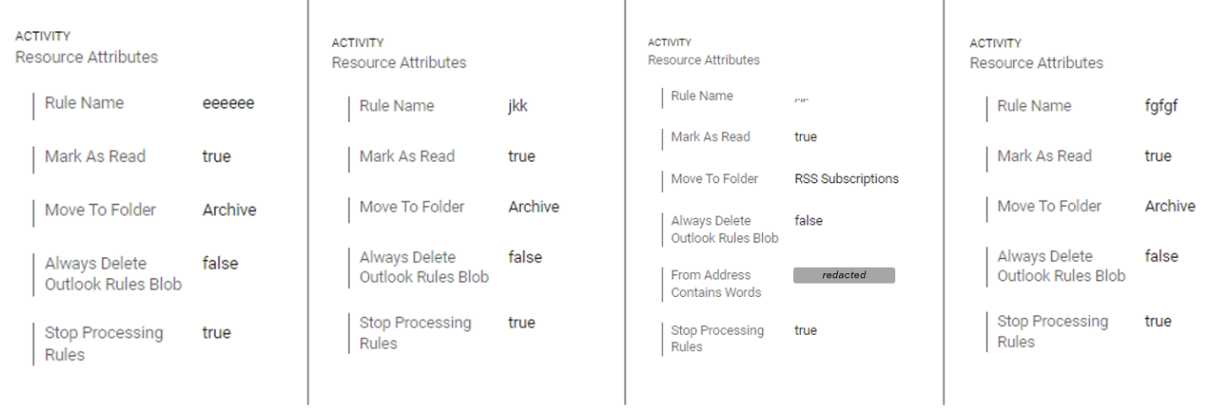
- Mailbox rules. Attackers create dedicated obfuscation rules intended to cover their tracks and erase all evidence of malicious activity from victims’ mailboxes.



 Loading comments...
Loading comments...
